Why Identity Management?
Because it is the foundation of IT security in your enterprise!
The comprehensive solution for provisioning identities and controlling access
Our consumer society is constantly changing and it is a difficult mission to keep pace with growing roles and requirements. With the proposed solution, we can quickly create and adapt new complex approvals and workflow implementations. It is easy to create a hierarchically structured database of identities that allows users to manage their core tasks without compromising IT security.
The product automates account creation and revocation, centralizes access administration and ensures every user has just one identity. It reduces the time, effort and cost of changes (such as when a user changes jobs within a company), protects against compliance violations by enforcing policy and controls, and makes it easy to immediately provision and revoke resources. It provides management of roles, policies, workflow and reporting to meet the most demanding scale and regulatory requirements
Challenges
- What does identity have? Everything in the network has identity: data, processes, devices, applications, web services, printers, servers, and more.
- Provisioning users can be a tedious, time-consuming, and costly effort. That effort, however, can pale in comparison to verifying that your provisioning activities have complied with your organization’s policies, requirements, and regulations
- Whether the right people have access to the right resources?
- Whether the wrong people have no access to the same resources?
- Whether an employee who got into work yesterday has access to the network, to his e-mail, and to a few other systems required for his job
- Is the access of an employee who left last week revoked?
The solution
It delivers a complete, yet affordable solution to ensure the right access to the right resources at the right time across your enterprise —both inside the firewall and into the cloud.
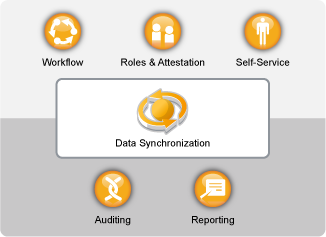
The core solution capabilities can help you automate the business processes in your organization. These capabilities—workflows, roles, attestation, self-service, auditing, and reporting—use multi-system data synchronization driven by your business policies to automate the processes involved in provisioning users and managing passwords, two of the most difficult and time-consuming duties of an IT organization.
The proposed solution simplifies the process of identity management. The management of access rights and the associated passwords throughout the lifecycle of a single user is automated:
- Provided access on the first business day
- Changing these rights throughout its lifecycle
- Synchronize multiple passwords into a "strong" password to access all systems
- Removing his or her rights when leaving
Industry regulations and audits put added pressure on a variety of enterprise departments and IT resources to pull together the information they need to be compliant. Your organization needs a comprehensive solution that efficiently simplifies and secures user identities and provisioning management while ensuring compliance
The proposed lets you provision users based on their roles in the organization. You define the roles and make the assignments according to your organizational needs. When a user is assigned to a role, the product provisions the user with access to the resources associated with the role.
The solution should ensure user productivity by giving users access to the resources they need, when they need them—and only up to the level they require to do their jobs
More than likely, user access to many of the resources in your organization doesn’t require anyone’s approval. However, access to other resources might be restricted and require approval from one or more individuals. The proposed solution provides workflow capabilities to ensure that your provisioning processes involve the appropriate resource approvers.
If your organization is like most, you have identity data stored in multiple systems. Or, you have identity data stored in one system that you could really use in another system. Either way, you need to be able to easily share and synchronize data between systems.
The solution lets you synchronize, transform, and distribute information across a wide range of applications, databases, operating systems, and directories.
As part of its data synchronization capability, the product can also help you synchronize passwords between systems. Whenever a user changes his or her password in one of the systems, It can synchronize that password to all other systems he/her has access rights to.
With deployment of the solution you can be sure that all of your user provisioning activities, past and present, are being tracked and logged for auditing purposes. It contains an intelligent repository of information about the actual state and the desired state of the Identity Vault and the managed systems within your organization. By querying the warehouse, you can retrieve all of the information you need to ensure that your organization is in full compliance with relevant business laws and regulations.
The solution contains predefined reports that let you perform queries against the Identity Information Warehouse to demonstrate compliance for business, IT, and corporate policies. You can also create custom reports if the predefined reports don’t meet your needs.
Benefits
- Automating complex processes to give immediate access to the necessary resources
- Provisioning the user with access based on its business role and company policies
- Password synchronization and provisioning single sign on
- Allows users to renew their passwords through web services if company policy permits
- Creating and enforcing "strict" password policies across the enterprise
- Notifications (alerts) when giving incorrect / non-compliant access rights
- Reduce the cost and complexity of maintenance